Blog
Comparing Digital and Quantum Computers, Part 9: Assesment of Original Attack
Everyone in the IT world is wondering how big a threat quantum computers pose to cryptography and how to deal with the problem. This series of articles tries to explain the problem in a popular way. After getting acquainted with the available technologies, it is possible to try to estimate the capabilities of quantum computers around 2035.
Technology overview
Based on this information, it is possible to create the following overview, which is again an estimate for the year 2035. To attack the following algorithms, a quantum computer, like a digital computer, needs a specific time, and in the case of a quantum computer, a minimum number of passes. This is followed by post-processing on a conventional digital computer. In addition to the specified time, it also requires a certain minimum number of qbits, but there is constant development in this area, so at the time of writing the article the result is slightly overestimated. For these requirements, the most significant input is probably the cooling power. Here is a modified table that takes into account the power consumption of individual qbits and gates in the range of pW, thermal radiation of the cabling of 1mW/m, and reading the state from one qbit of 100mW. The system mentioned assumes high-quality insulation and the need for cooling to a temperature of 1 mK , and uses a steel supporting structure with mechanical parameters for the weight of the device corresponding to a steel ball of a given volume. The need for internal cooling for heat dissipation is deliberately neglected, this is only a theoretical model. The necessary construction for heat dissipation would extremely change the conditions of the entire approximate calculation. The resulting energy stated is needed for the implementation of one calculation, not all repetitions to ensure an adequate level of probability. At the same time, it does not include post-processing, which, on the other hand, does not have significant power requirements.
| Algorithm | Logical qubits | Number of gates | Time (s) | Volume (m3) | Energy (J) |
| DSA 1024 | 2058 | 1.074·1010 | 1.074·103 | 0.028 | 1.667·1014 |
| DSA 2048 | 4106 | 8.590·1010 | 8.590·103 | 0.055 | 2.661·1015 |
| DH 1024 | 2058 | 1.074·1010 | 1.074·103 | 0.028 | 1.667·1014 |
| DH 2048 | 4106 | 8.590·1010 | 8.590·103 | 0.055 | 2.661·1015 |
| DH 3072 | 6154 | 2.899·1011 | 2.899·104 | 0.083 | 1.346·1016 |
| DH 4096 | 8202 | 6.872·1011 | 6.872·104 | 0.111 | 4.252·1016 |
| DH 6144 | 12298 | 2.319·1012 | 2.319·105 | 0.166 | 2.152·1017 |
| DH 8192 | 16394 | 5.498·1012 | 5.498·105 | 0.221 | 6.800·1017 |
| brainpoolP256r1 | 522 | 1.678·108 | 16.78 | 0.007 | 6.607·1011 |
| brainpoolP384r1 | 778 | 5.662·108 | 56.62 | 0.010 | 3.324·1012 |
| brainpoolP521r1 | 1052 | 1.414·109 | 141.42 | 0.014 | 1.122·1013 |
| NIST P-256 | 522 | 1.678·108 | 16.78 | 0.007 | 6.607·1011 |
| NIST P-384 | 778 | 5.662·108 | 56.62 | 0.010 | 3.324·1012 |
| NIST P-521 | 1052 | 1.414·109 | 141.42 | 0.014 | 1.122·1013 |
| Curve25519 | 520 | 1.658·108 | 16.58 | 0.007 | 6.505·1011 |
| Curve448 | 906 | 8.992·108 | 89.92 | 0.012 | 6.146·1012 |
| RSA 512 | 1029 | 6.711·108 | 67.11 | 0.014 | 5.210·1012 |
| RSA 1024 | 2053 | 5.369·109 | 536.87 | 0.028 | 8.316·1013 |
| RSA 2048 | 4101 | 4.295·1010 | 4.295·103 | 0.055 | 1.329·1015 |
| RSA 2540 | 5085 | 8.194·1010 | 8.194·103 | 0.069 | 3.143·1015 |
| RSA 3072 | 6149 | 1.450·1011 | 1.450·104 | 0.083 | 6.725·1015 |
| RSA 4096 | 8197 | 3.436·1011 | 3.436·104 | 0.110 | 2.125·1016 |
| RSA 7168 | 14341 | 1.841·1012 | 1.841·105 | 0.193 | 1.992·1017 |
| RSA 8192 | 16389 | 2.749·1012 | 2.749·105 | 0.221 | 3.399·1017 |
| RSA 13550 | 27105 | 1.244·1013 | 1.244·106 | 0.365 | 2.544·1018 |
| RSA 37100 | 74205 | 2.553·1014 | 2.553·107 | 1.000 | 1.429·1020 |
| RSA 76608 | 153221 | 2.248·1015 | 2.248·108 | 2.064 | 2.599·1021 |
The article contains only an estimate, not a specific implementation. It is not even an optimal estimate, because the development of algorithms for quantum computers will accelerate attacks. Algorithms are already significantly simpler, but their explanation is challenging and it is extremely difficult to find a suitable idea. The question is to what extent the risks arising from quantum computers are overestimated in terms of the time frame. Another issue is the effect of multiplexing, where several qubits use one gate. While this reduces the required number of gates (connections) and their power consumption, the total processing time is also increased in the corresponding proportion. An attack using quantum computers is definitely within the capabilities of the entire human civilization, and perhaps even within the capabilities of some state actors. Nevertheless, it can be somewhat problematic to attack even simpler elliptic curves for a simple reason. This reason is to ensure an adequate amount of available energy. In addition to the design difficulties, a cryptographically relevant quantum computer will also have a problem with the aforementioned power source. According to this basic description, an attack on asymmetric algorithms could require significant investment in resources. On the other hand, increasing the operating temperature by a single order of magnitude will significantly reduce the aforementioned impacts. Added to this is the question of how to solve the problem of waste heat. According to this estimate, quantum computers are still a theoretical attack. However, this attack may become feasible in the foreseeable future, where any technological breakthrough threatens current cryptography.
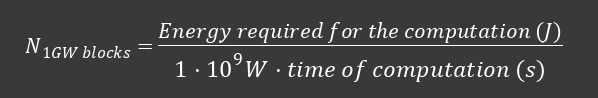
If, based on the above results, I were to consider power supply using blocks with 1GW reactors for simplicity, I would get the following results. For Curve25519 , brainpoolP256r1 and NIST P-256, it would be 39 blocks, for brainpoolP384r1 and NIST P-384, it would be 58 blocks, for Curve448, it would be 60. blocks and for brainpoolP521r1 and NIST P-521 even 78 blocks.I'm really curious to see how close this estimate will be to reality. Given the possibilities offered by quantum computers, I'd like to be wrong.
At the same time, the above overview shows that for small key sizes, a classical digital computer could be more suitable for decryption than a quantum computer. Examples include DSA 1024b, DH 1024, DSA 2048b and DH 2048b. For small key sizes of the RSA algorithm, this difference is not so great, quantum computers have dominated here from the beginning. For large keys, of course, the quantum computer has a clear advantage in all cases. The biggest problem here is cooling, the temperature close to absolute zero is as limiting as the speed of light. The goal of the development is therefore to shift the operating temperatures of the system to more comfortable temperature ranges. Here is an overview of what this would mean in terms of energy consumption, i.e. the energy required for one calculation.
| Algoritmus | 1μK (J) | 1mK (J) | 0,1K (J) | 1K (J) | 10K (J) | 100K (J) |
| DSA 1024 | 1.667·1017 | 1.667·1014 | 1.667·1012 | 1.667·1011 | 1.667·1010 | 1.667·109 |
| DSA 2048 | 2.661·1018 | 2.661·1015 | 2.661·1013 | 2.661·1012 | 2.661·1011 | 2.661·1010 |
| DH 1024 | 1.667·1017 | 1.667·1014 | 1.667·1012 | 1.667·1011 | 1.667·1010 | 1.667·109 |
| DH 2048 | 2.661·1018 | 2.661·1015 | 2.661·1013 | 2.661·1012 | 2.661·1011 | 2.661·1010 |
| DH 3072 | 1.346·1019 | 1.346·1016 | 1.346·1014 | 1.346·1013 | 1.346·1012 | 1.346·1011 |
| DH 4096 | 4.253·1019 | 4.253·1016 | 4.253·1014 | 4.253·1013 | 4.253·1012 | 4.253·1011 |
| DH 6144 | 2.152·1020 | 2.152·1017 | 2.152·1015 | 2.152·1014 | 2.152·1013 | 2.152·1012 |
| DH 8192 | 6.800·1020 | 6.800·1017 | 6.800·1015 | 6.800·1014 | 6.800·1013 | 6.800·1012 |
| brainpoolP256r1 | 6.607·1014 | 6.607·1011 | 6.607·109 | 6.607·108 | 6.607·107 | 6.607·106 |
| brainpoolP384r1 | 3.324·1015 | 3.324·1012 | 3.324·1010 | 3.324·109 | 3.324·108 | 3.324·107 |
| brainpoolP521r1 | 1.122·1016 | 1.122·1013 | 1.122·1011 | 1.122·1010 | 1.122·109 | 1.122·107 |
| NIST P-256 | 6.607·1014 | 6.607·1011 | 6.607·109 | 6.607·108 | 6.607·107 | 6.607·106 |
| NIST P-384 | 3.324·1015 | 3.324·1012 | 3.324·1010 | 3.324·109 | 3.324·108 | 3.324·107 |
| NIST P-521 | 1.122·1016 | 1.122·1013 | 1.122·1011 | 1.122·1010 | 1.122·109 | 1.122·107 |
| Curve25519 | 6.505·1014 | 6.505·1011 | 6.505·109 | 6.505·108 | 6.505·107 | 6.505·106 |
| Curve448 | 6.146·1015 | 6.146·1012 | 6.146·1010 | 6.146·109 | 6.146·108 | 6.146·107 |
| RSA 512 | 5.210·1015 | 5.210·1012 | 5.210·1010 | 5.210·109 | 5.210·108 | 5.210·107 |
| RSA 1024 | 8.316·1016 | 8.316·1013 | 8.316·1011 | 8.316·1010 | 8.316·109 | 8.316·108 |
| RSA 2048 | 1.329·1018 | 1.329·1015 | 1.329·1013 | 1.329·1012 | 1.329·1011 | 1.329·109 |
| RSA 2540 | 3.143·1018 | 3.143·1015 | 3.143·1013 | 3.143·1012 | 3.143·1011 | 3.143·1010 |
| RSA 3072 | 6.725·1018 | 6.725·1015 | 6.725·1013 | 6.725·1012 | 6.725·1011 | 6.725·1010 |
| RSA 4096 | 2.125·1019 | 2.125·1016 | 2.125·1014 | 2.125·1013 | 2.125·1012 | 2.125·1011 |
| RSA 7168 | 1.992·1020 | 1.992·1017 | 1.992·1015 | 1.992·1014 | 1.992·1013 | 1.992·1012 |
| RSA 8192 | 3.399·1020 | 3.399·1017 | 3.399·1015 | 3.399·1014 | 3.399·1013 | 3.399·1012 |
| RSA 13550 | 2.544·1021 | 2.544·1018 | 2.544·1016 | 2.544·1015 | 2.544·1014 | 2.544·1013 |
| RSA 37100 | 1.429·1023 | 1.429·1020 | 1.429·1018 | 1.429·1017 | 1.429·1016 | 1.429·1014 |
| RSA 76608 | 2.599·1024 | 2.599·1021 | 2.599·1019 | 2.599·1018 | 2.599·1017 | 2.599·1016 |
In this series, I tried to explain the problems of attacks on current asymmetric cryptography and to explain in a somewhat popular way the problems of attacks using quantum computers and the Shorr algorithm. Although the part dedicated to quantum computers tries to explain the mentioned issue, it is mainly a popular form and includes some distortion of information, for which I apologize. This area is extremely complex and its explanation is difficult. In my opinion, however, it is necessary to draw attention to the publicly overlooked problem of attack time depending on the need to achieve a certain accuracy and, in the case of cryogenic devices, the need to effectively cool such devices.
In the future, this series will be loosely followed by a critical assessment of the successes of attacks on asymmetric cryptography using both classical computers (history) and quantum computers. The reason is an effort to draw attention to what I believe to be misleading experiments and their possible inappropriate interpretation. I would like to compute power needed for each quantum algorithms also.




